For some people is hard to imagine a world where people would rely on stealing wireless to have access to the internet, and I’m right there with them. To find out if someone is stealing your Wi-Fi it’s not a hard process but it can get complicated. That’s why I have made this article to help you out in completing this process.
The internet nowadays is essential and in some cases, speed is important too. When you have a wireless router people would get tempted to try and guess your password and the more people use your internet the less speed you get. In a world where we have easy access to the free public internet, 4G, and now 5G I find it really difficult to understand people that steal their neighbor’s Wi-Fi.
Although we use mobile data on our smartphones when we are out and about in the world, Wi-Fi still dominates in a home environment, coffee shops, public malls, and a lot more. This happens because the technology of Wi-Fi is faster and cheaper also without the limiting bandwidth caps of cellular data it can easily transform a zone into Wi-Fi free. Most people nowadays also have Wi-Fi routers in the homes instead of a regular wired one and this has opened us up the possibility of our neighbors stealing Wi-Fi. This is we don’t take the necessary measurements to secure our network.
If you suspect someone is using your internet without permission or piggybacking then you have come to the right place to find out the truth. On some rare occasions, these people can also inject a virus on your network and try to steal information, but we can easily defend against that also. Follow the article to find out how to protect yourself.
Learn How your Wi-Fi Network Works
If you want to catch someone who is eating all your valuable bandwidth data then first you will need to have a slight understanding of the wireless Network and how it works. A wireless network is made of a broadhead internet connection from a cable or modem. The modem is attached to the wireless router and that’s what distributes the signal and creates what we call a network.
Your personal network is referred to as a LAN or Local Area Network. In the LAN you can set up your devices such as your laptop, computer, printer, mobile phones, etc. Your router has a feature called the Dynamic Host Client Protocol or DHCP. This has a list of the allowed devices in your LAN and also specifies the IP address automatically.
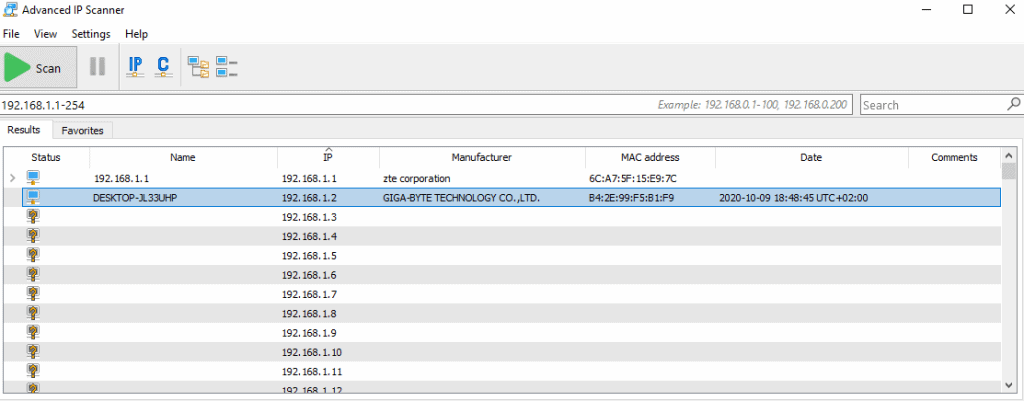
You should know by now that each device does not only have a unique IP address but also a MAC address. A MAC address is called a Media Access Control, this serves as the unique signature of the device. So with these two things the IP Address and the MAC address of the device you can easily figure out if there’s an imposter on your network.
How to Secure your Network
If you have seen signs of your internet speed slowing down and you have checked out all the other reasons such as the ISP having issues, the website overloaded with traffic, or even long distance from the router. Then probably someone is using your internet bandwidth without your permission. This might have happened because you had a weak password in place such as ‘12345678’ or something more common nowadays ‘20202020’. If you don’t have a password at all I honestly don’t know what to say to you other than it’s entirely your fault. If that’s not the case then you might have configured your network in a weak manner and that’s what we are going to try and fix now.
Change The Passwords
One of the most basic elements of security is having a password and you can change that simply from a web browser connected to that network. Most Wi-Fi routers are accessible with the following address http://192.168.1.1 also they almost always use the same login credentials since that’s how it comes from the manufacturer. They combine words like ‘root’ and ‘admin’ with a generic password or just the same word twice. But if we know this wouldn’t the other people who try to steal your network already know this as well? The answer is yes and this is what we should change to add a layer of security to our network.
Now you can do this step before someone else does get in your network. Change the router’s login credentials to anything other than ‘admin’ and also change the password to something more complex. The best practices for a secure password is to be over the length of 8 characters, to use symbols and numbers. This should also be the same for your Wi-Fi password and once you have done these two steps you are the most secure that you can get. Just like I said in the beginning of this article is not hard to secure your network you just need to know what to do.
How to Detect Someone on Your Network?
With the measures that we suggested you take in the above segment, there is almost no possible way for a normal user to get into your network. But anyway let’s learn how you can spot out someone stealing your wireless if you don’t take the measures to prevent it from happening. I talked briefly about the importance of the IP address and the MAC address now let’s get into it. Every device that connects to your network will have these addresses and if you see a device that is not one that you own then you know that there is someone else stealing Wi-Fi.
You can perform a network IP check from a bunch of different software online but I would suggest Advanced IP Scanner. I have used this tool on multiple different occasions and it has always delivered. It’s simple to use and the intuitive GUI will help you a lot. From this tool you can select the range of which the program needs to search through your network and after the scan is finished it will show the IPs and MAC addresses of the devices that it finds. To make your job easier once you know which ones are your devices you can name them accordingly so when the next time you scan you will find the unrecognized device easily.
Closing Thoughts
Wi-Fi stealing nowadays is not that big of an issue anymore but it’s still important that you know what is happening with your network. Some of the things that we have mentioned in this article like changing the router credentials are considered by many as good practices whenever setting up a network. So if want to have the best security and follow good practice it’s recommended by many IT specialists that you do those things. I hope this article helped you find the intruder on your network and if you have anything to ask leave a question down below in the comments.